39 antivirus approaches in network security
15 Best Network Security Auditing Tools for 2022 - Comparitech 11. Acunetix. Acunetix is a web application security scanner and one of the top network security auditing software that can test for over 50,000 network vulnerabilities when integrated with OpenVAS. It discovers issues like open ports that leave your systems open to being compromised. Network security essentials, a multi-layered approach for 2022 See this guide to email security. Modern network security essentials include email solutions. Hyperscale network security. Hyperscale refers to an architecture's capacity to scale appropriately in accordance with increased system demands. Hyperscale network security can help organizations meet new business and networking requirements.
Use a zero-trust approach to network security | Total Defense Use a zero-trust approach to network security. If you manage an enterprise-grade network, you're likely responsible for keeping sensitive corporate data under lock and key. When employees and outsiders access your corporate network, they could also potentially access unprotected data. Zero-Trust Network Access verifies the identity of a user ...

Antivirus approaches in network security
Learn about 4 approaches to comprehensive security that help leaders be ... Advantech's security team is now looking to further raise visibility into their IoT and OT risk with agentless, network-layer security provided by Microsoft Defender for IoT—including asset discovery, vulnerability management, and continuous threat monitoring with anomaly detection. "We didn't have staff dedicated to figuring out our ... Network security and containment in Azure | Microsoft Docs This works to protect and contain East-West traffic within your cloud network infrastructure. An important network security design decision is to use or not use host-based firewalls. Host-based firewalls support a comprehensive defense in-depth strategy. However, to be of most use they require significant management overhead. What is Network Security: Its Types and Management - Software Testing Help In the above figure, it has been explained that computers with strong passwords, updated security features, and equipped with anti-virus software protection are immune to a worm attack. On the other hand, computers or networks with a weak password, a date system update, and are not equipped with anti-virus software are more susceptible to the attacks of worms and easily get corrupted and diminished.
Antivirus approaches in network security. Four benefits of a software-defined approach to network security One major advantage of a software-defined zero trust approach is that it enables uniform protection, regardless of whether a resource is located in the cloud or on-premise — or if it moves from on-premise to the cloud or even when moving between multiple clouds. Moving applications and data to the cloud — or multiple clouds — effectively ... 13 Best Network Security Tools for 2022 (Paid & Free) - Comparitech It installs on Windows, Linux, macOS, and Free BSD. OWASP ZAP A web application security system that scans web pages for known threats and examined web servers for configuration and access control weaknesses. Zscaler Cloud Firewall A cloud-based network security service that is ideal for virtual offices. 10 BEST Network Security Software [2022 TOP SELECTIVE ONLY] Norton Security is known for being a multi-device and multi-OS antivirus software. Therefore, it offers various features for real-time protection against malware, viruses, spyware, and other digital threats that can infiltrate your system through your network. Top 10 Common Types of Network Security Attacks Explained - EC-Council 5. Botnet. Botnets comprise the network of compromised systems connected to the Internet. The hacker gains access to all these devices on the network and manipulates the bots to send spam, perform data theft and enable DDoS (Distributed Denial of Service) attacks. 6. DoS (Denial of Service) and DDoS Attacks.
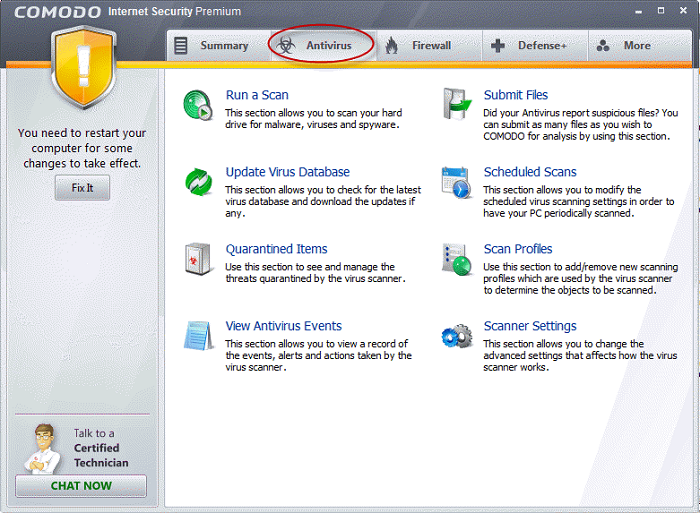
The Best Antivirus Software for 2022 | PCMag With McAfee AntiVirus Plus, one subscription lets you install security software on every Windows, macOS, Android, and iOS device in your household. When all your devices are armored against attack ... Antivirus Approaches EDR vs Enterprise Antivirus: What's the Difference? These two approaches to security are fundamentally different, and only one is appropriate for dealing with modern threats. Features of Antivirus Back in the days when the number of new malware threats per day could comfortably be counted in a spreadsheet document, Antivirus offered enterprises a means of blocking known malware by examining ... Difference between Antivirus and Internet Security Antivirus: Antivirus is an application or software which provides security from the malicious software coming from the internet. An antivirus chases the method in which it performs 3 actions which are: 1. Detection 2. Identification 3. Removal . Antivirus deals with both external threats and internal threats.
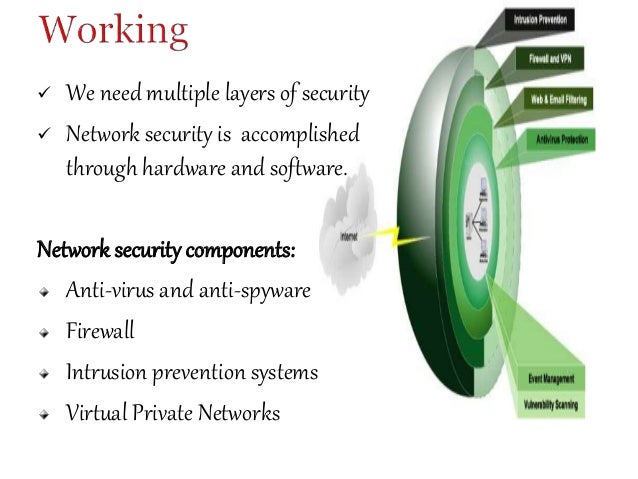
5 Threat And Risk Assessment Approaches for Security Professionals in ... 1. The Security Threat and Risk Assessment. To people who work in the security or protection industry, threat assessment is the first step in a risk and vulnerability analysis. This threat assessment task involves assessing the various security risks associated with a particular location. What Is Next-Gen Antivirus and Why Do You Need It? | Impact Networking Next-gen antivirus uses a combination of modern technology including machine learning and artificial intelligence to more effectively identify and remove threats. This is achieved by taking an approach that focuses on behavior—NGAV uses algorithms which examine processes, data, application use, network activity, and end-user behavior to ... How Does Antivirus Software Work? | 2022 | U.S. News Antivirus software isn't one thing, but rather a package of evolving defense mechanisms designed to protect your computer against the constant barrage of known, unknown, and ever-shifting ... Network Security - GeeksforGeeks Network Security refers to the measures taken by any enterprise or organization to secure its computer network and data using both hardware and software systems. This aims at securing the confidentiality and accessibility of the data and network. Every company or organization that handles a large amount of data, has a degree of solutions against many cyber threats.
Systems Security: Firewalls, Encryption, Passwords & Biometrics There are a number of different approaches to computer system security, including the use of a firewall, data encryption, passwords and biometrics. Firewall One widely used strategy to improve ...
Malicious software. Attacks and countermeasures,II Antivirus ... Antivirus Approaches. • Prevention : do not allow a virus to get into the system (in general, impossible to achieve);. • Detection: once infection has ...4 pages
What is Antivirus and How Does a Virus Scanner Work? - VPNoverview.com An antivirus program is a software program that protects your computer, laptop, tablet, phone, or other internet connected device against malware. Antivirus software, also known as a virus scanner, identifies viruses and subsequently stops and removes them. Over the years, malware has changed and has grown. Malicious programs have become more ...
Network Security vs. Cybersecurity: Which Career Path to Choose - SMU Various sources approach the network security vs. cybersecurity question differently. Some assert that cybersecurity is a skill cluster comprising more than 120 distinct skills—one of which is network security—while network security refers to policies and practices that prevent unauthorized access to or misuse of computer networks ...
5 Different Approaches to Maintaining Cyber Security Security Processes That can be Automated. Automation can manage the tedious and crucial aspects of a cyber security framework. Below are the five processes that can benefit from security automation. Monitoring and detecting threats: Businesses should be able to see all the areas of the IT environment all the time.
What is Network Security? Definition, Best Practices & Risks - CrowdStrike Next-generation antivirus (NGAV) is a network security tool that uses a combination of artificial intelligence, behavioral detection, machine learning algorithms and exploit mitigation, so known and unknown threats can be anticipated and immediately prevented.
Control Engineering | Changing a network security approach Changing a network security approach Most organizations rely heavily on security architects to vet products and assemble optimal solutions that align with security, technology, and business requirements, but a different approach is needed in manufacturing facilities. By MediTechSafe July 30, 2021. Facebook; Twitter;
What is Layered Security & How Does it Defend Your Network? Firewall. The first line of defense in your network security, a firewall monitors incoming and outgoing network traffic based on a set of rules. A firewall acts as a barrier between a trusted network and an untrusted network, only allowing into your network traffic that has been defined in the security policy. Patch Management.
Differences between Network & Web Application Security. Comparing ... Historically, a greater emphasis has been placed on network security, and this is an approach that has worked well. However, as the trend towards depending more on increasingly complicated web applications and improved access to information continues, it has become critically important to manage all aspects of security — reducing overall risk ...
What are the approaches of Information Security Models? - Tutorials Point This is a secure approach, but the difficulty is that it cannot scale well. The difficulty and diversification of current sites/organizations creates the service even harder. Network Security − Host security is complex to obtain as organizations become larger and develop into more diverse. In this approach, the target is to control network ...
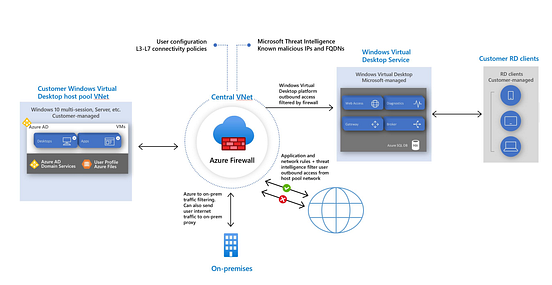
Network security concepts and requirements in Azure The advantage of this approach is that the VPN connection is established over the Azure network fabric, instead of connecting over the internet. This provides you an extra layer of security, compared to site-to-site VPNs that connect over the internet. ... Microsoft Cloud Services and Network Security; Azure DDoS protection. Distributed denial ...
What is Network Security: Its Types and Management - Software Testing Help In the above figure, it has been explained that computers with strong passwords, updated security features, and equipped with anti-virus software protection are immune to a worm attack. On the other hand, computers or networks with a weak password, a date system update, and are not equipped with anti-virus software are more susceptible to the attacks of worms and easily get corrupted and diminished.
Network security and containment in Azure | Microsoft Docs This works to protect and contain East-West traffic within your cloud network infrastructure. An important network security design decision is to use or not use host-based firewalls. Host-based firewalls support a comprehensive defense in-depth strategy. However, to be of most use they require significant management overhead.
Learn about 4 approaches to comprehensive security that help leaders be ... Advantech's security team is now looking to further raise visibility into their IoT and OT risk with agentless, network-layer security provided by Microsoft Defender for IoT—including asset discovery, vulnerability management, and continuous threat monitoring with anomaly detection. "We didn't have staff dedicated to figuring out our ...






![[PDF] Intelligence-Driven Computer Network Defense Informed by Analysis ...](https://d3i71xaburhd42.cloudfront.net/e67025655c9a99eb88dd89d1f297d1f43c3b83f6/8-Figure5-1.png)


![[PDF] Intelligence-Driven Computer Network Defense Informed by Analysis ...](https://d3i71xaburhd42.cloudfront.net/e67025655c9a99eb88dd89d1f297d1f43c3b83f6/5-Table1-1.png)

0 Response to "39 antivirus approaches in network security"
Post a Comment